Automated Security Scanning
Set it and forget it. Schedule vulnerability scans to run daily, weekly, or monthly — automatically.
Scan queue
Next scheduled in 2h 14m · 11 scanners active
Scan scheduling
Configure scans to run on your schedule. Choose daily, weekly, or monthly intervals — or set up custom cron-based schedules for precise control.
- Flexible cron-based scheduling for any interval
- Per-asset scan schedules — different frequencies for different assets
- Timezone-aware scheduling to scan during off-peak hours
Scan types
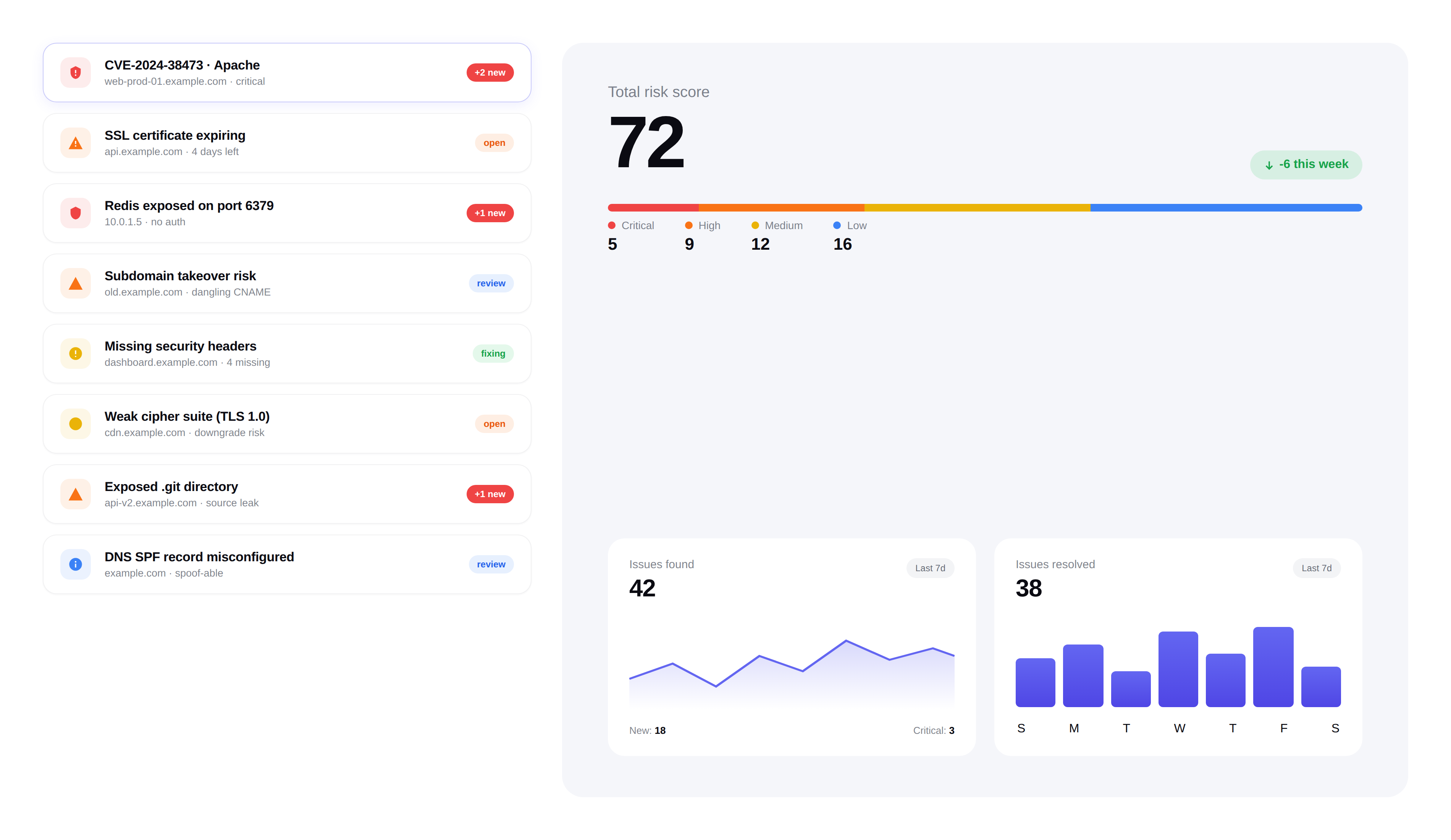
FortWatch runs multiple scan types against your assets, each designed to uncover different categories of security issues.
- Vulnerability Scanning:Detect known CVEs, misconfigurations, and security weaknesses
- Port Scanning:Discover open ports and running services across your infrastructure
- SSL Analysis:Check certificate validity, cipher strength, and protocol support
- Cloud Security:Identify misconfigurations and exposed services in cloud environments
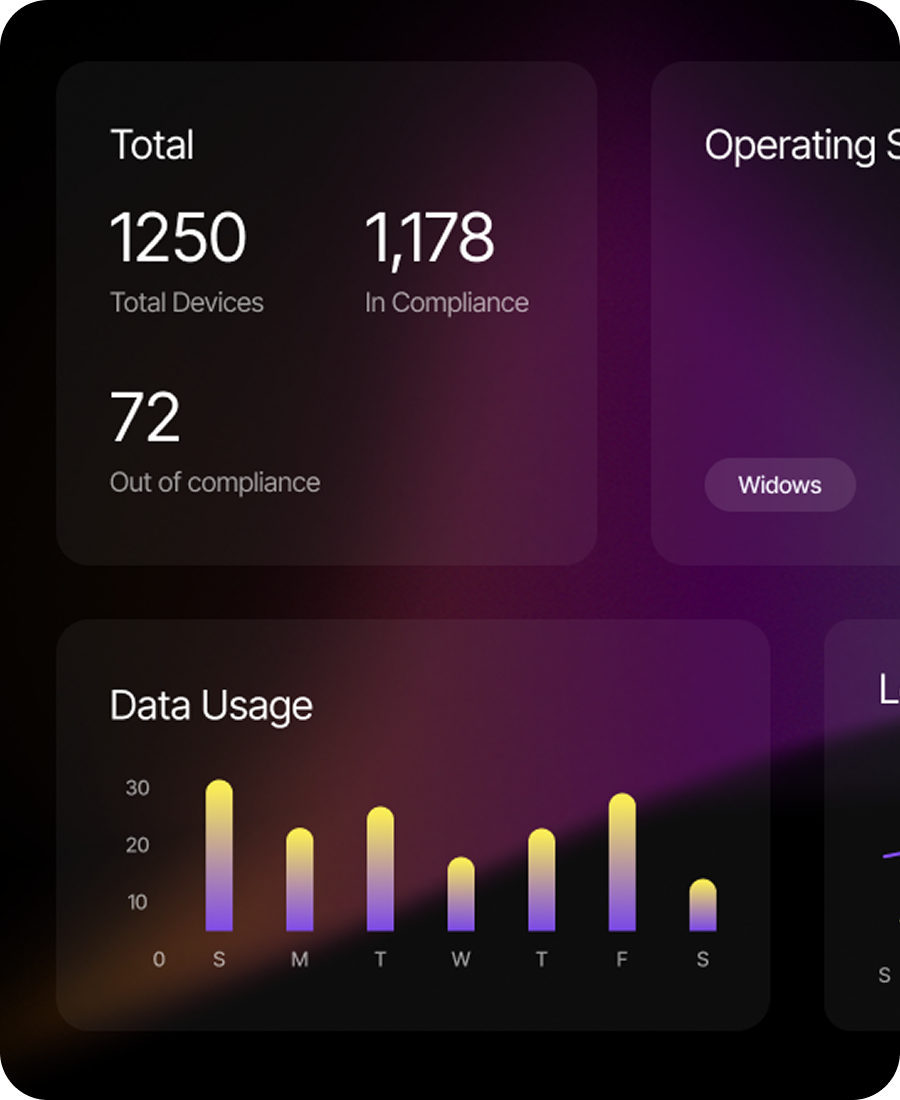
Parallel scanning
Scan multiple assets simultaneously without waiting in a queue. FortWatch's scanning infrastructure handles parallel workloads efficiently.
- Concurrent scanning across multiple assets
- Intelligent queue management to prevent resource contention
- Real-time scan progress tracking from the dashboard
Scan history
Every scan is logged with full results. Compare findings across scan runs to track your security posture over time.
- Complete history of all scan runs with timestamps
- Diff view showing new, resolved, and unchanged findings
- Export scan results for compliance documentation
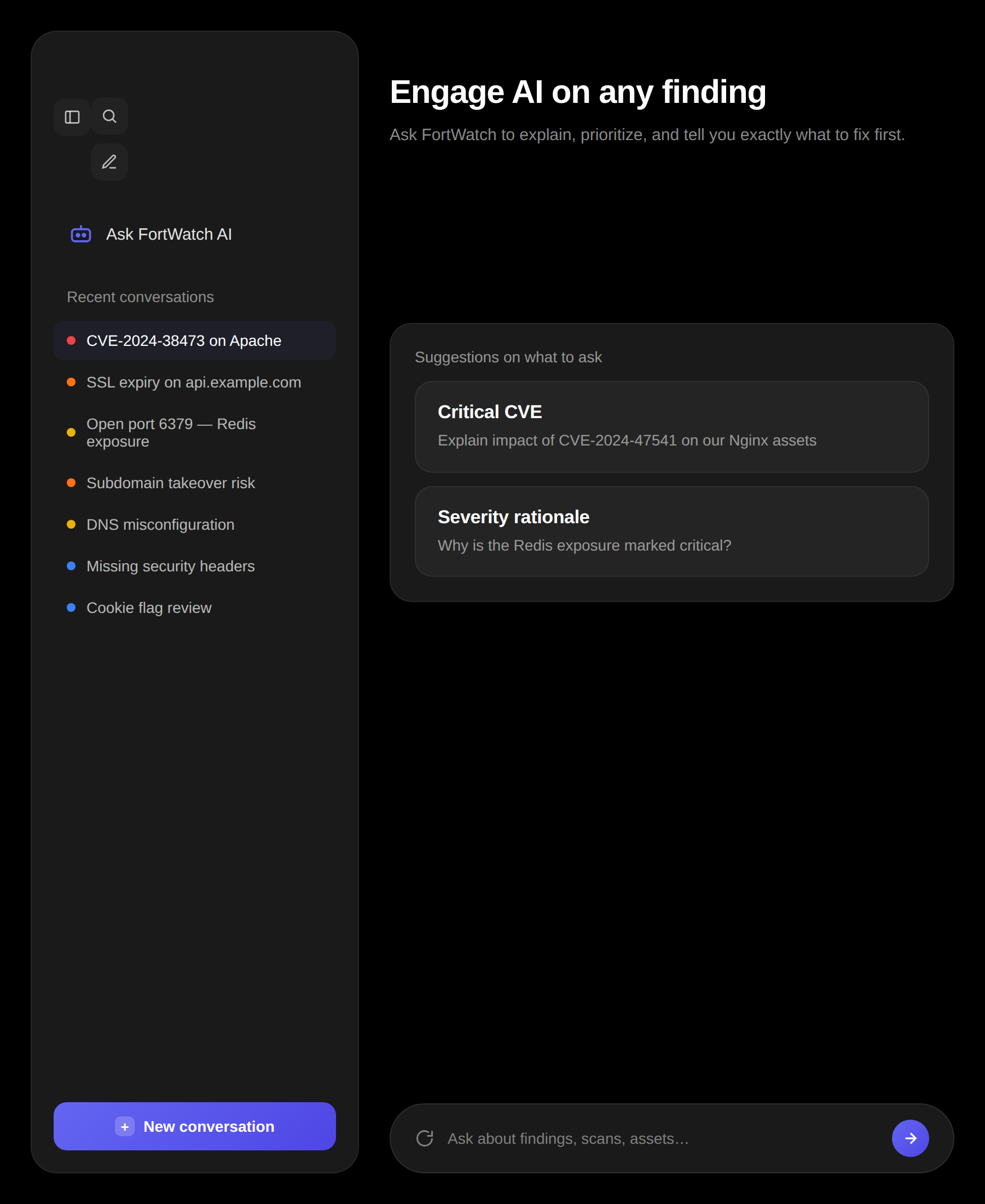
Hands-off security
Once configured, FortWatch continuously monitors your infrastructure without manual intervention. You only need to act when something needs fixing.
- Zero manual effort after initial setup
- Automatic alerting when new issues are found
- AI-powered summaries after every scan run
Frequently asked questions
Answers to the most common questions about automated scans, schedules, and scan behavior.
How often do automated scans run in FortWatch?+
FortWatch runs on the schedule you set. Most customers run weekly full scans with daily lightweight checks on critical assets, but you can pick daily, weekly, monthly, or a custom cron expression per asset. If you want continuous coverage, schedule overlapping scanners so there's always fresh data — port discovery one day, CVE scanning the next, SSL checks the day after.
Can I schedule scans for specific times or off-peak hours?+
Yes. Every schedule is timezone-aware and supports cron expressions, so you can run scans at 2 a.m. local time, only on weekends, or during your regular maintenance window. Per-asset overrides let you run noisy scanners on low-traffic assets and quiet scanners on production without touching a single config file.
What's included in each automated scan?+
A full FortWatch scan runs across 11 scanners covering CVE detection, open port discovery, service fingerprinting, SSL/TLS certificate and cipher analysis, DNS and email security records, cloud exposure checks, subdomain enumeration, web exposure, HTTP security headers, directory brute force, and technology fingerprinting. Each scanner produces findings that are deduplicated, severity-tagged, and AI-triaged before you see them.
Will automated scanning slow down my production systems?+
FortWatch scans external attack surface, so scanners hit public endpoints the same way any internet user would. Rate limiting is built in per asset, and aggressive scanners (directory brute force, web exposure) are off by default. You can cap concurrency per workspace, and scheduled scans default to off-peak windows so legitimate traffic always takes priority.
How does FortWatch handle false positives?+
Every finding is run through AI triage before it reaches your dashboard — context from the asset, the CVE, and the actual response is checked for known false-positive patterns. You can also mark findings as false positive once, and FortWatch suppresses the same signature on future scans for that asset. Suppressions are audited, so nothing gets silently hidden.
How long does an automated scan take to complete?+
A single-asset scan typically finishes in 3 to 15 minutes depending on which scanners are enabled and how large the target is. Port scanning and CVE detection are the fastest; directory brute force and subdomain enumeration are the slowest. Parallel scanning means adding more assets doesn't linearly add time — a 20-asset scan usually completes in under an hour.
Can I trigger a manual scan outside the schedule?+
Yes. Any Owner, Admin, or Manager can run an on-demand scan from the asset page with one click. Manual scans don't interrupt the schedule — they run in parallel, and results are merged into the scan history. This is useful after a deployment, a certificate rotation, or when you're verifying a fix.
What happens when a scheduled scan finds a new vulnerability?+
FortWatch diffs the new scan against the previous one, flags net-new findings, and sends alerts based on severity. Critical and high findings trigger email or webhook notifications immediately; medium and low findings appear in the daily digest. Every finding includes an AI-written explanation, affected asset context, and a remediation suggestion so you can act without leaving the dashboard.
Secure your entire stack today
Start scanning in under 5 minutes. No credit card required. 14-day free trial included.