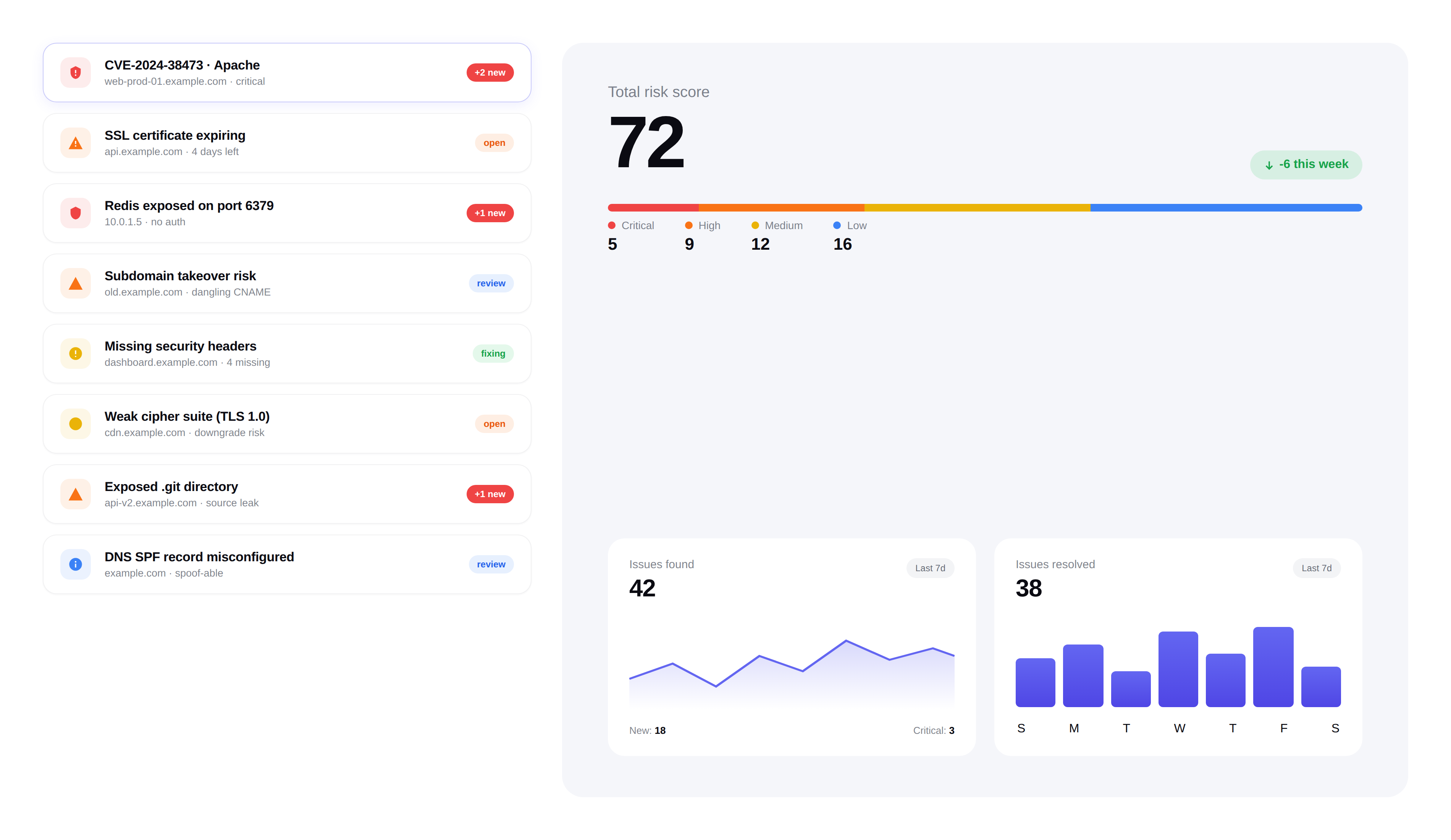
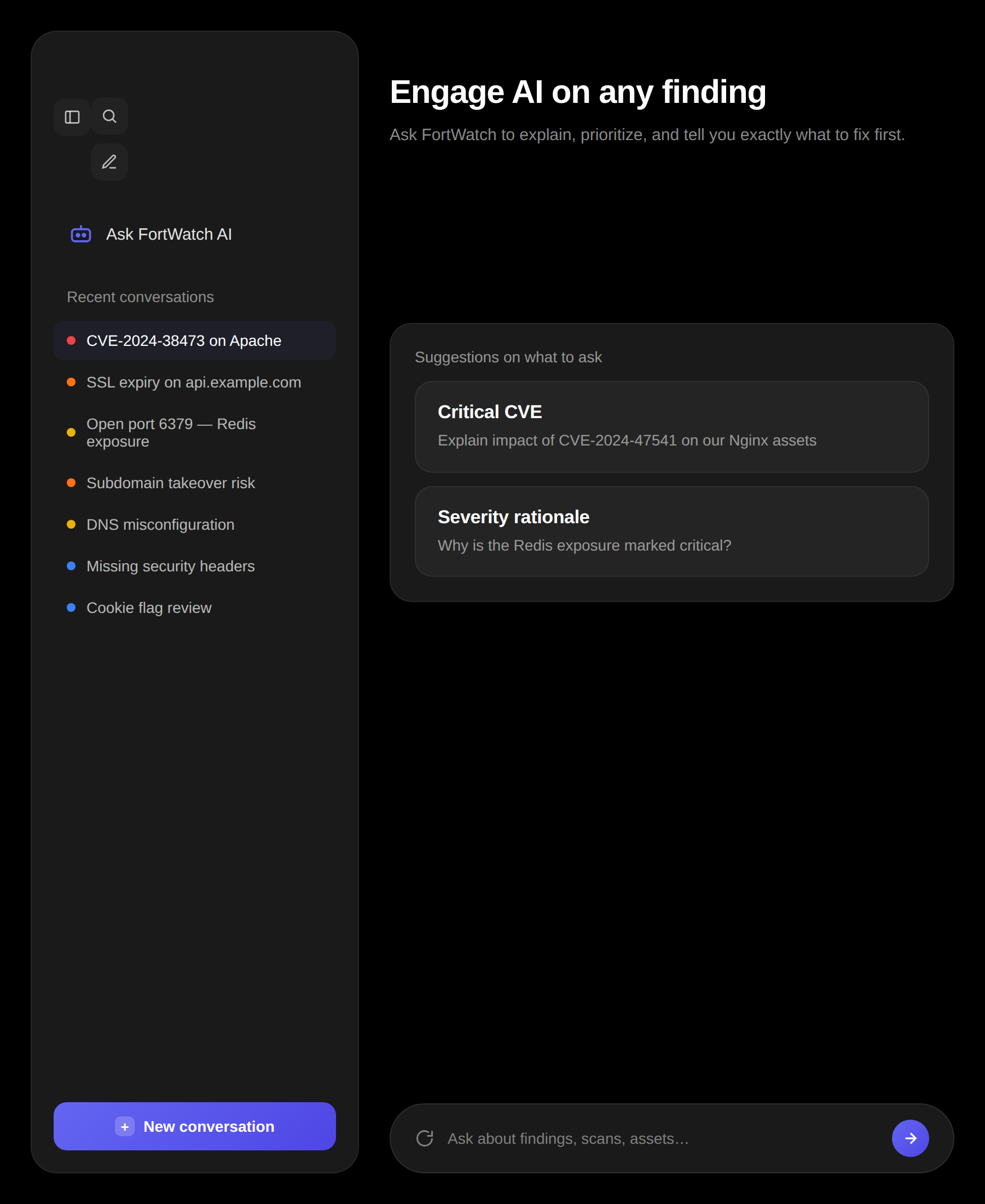
Real-time Security Alerts
Get notified the moment something changes. New vulnerabilities, port changes, SSL expirations — delivered instantly.
Recent alerts
12 today · 2 unread
- S
Critical: new CVE-2026-1847 affects api.example.com
#security-alerts · 2m ago
High: SSL cert on portal.example.com expires in 7 days
sarah@example.com · 1h ago
Medium: 3 missing HTTP security headers
https://alerts.example.com/hook · 3h ago
- S
High: subdomain takeover detected on forgot.example.com
#security-alerts · yesterday
- P
Critical: exposed .env file on legacy.example.com
critical-findings · 2d ago
Alert channels
Receive alerts wherever your team works. FortWatch delivers notifications through multiple channels so nothing falls through the cracks.
- Email notifications with detailed finding context
- Slack integration for instant team visibility
- Webhooks for custom integrations and automation
Alert types
Stay informed about every meaningful change across your infrastructure. FortWatch monitors for the events that matter most.
- New Findings:Instant notification when new vulnerabilities are discovered
- Port Changes:Alerts when new ports open or existing ports close unexpectedly
- SSL Expiry:Advance warnings before SSL certificates expire
- Scan Completions:Summary notifications when scheduled scans finish
Custom rules
Not every alert deserves your attention. Create custom rules to filter notifications by what matters to your team.
- Filter by severity — only get alerted on critical and high findings
- Filter by asset — monitor specific domains or IPs
- Filter by category — focus on the vulnerability types you care about
Alert history
Every alert is logged and searchable. Review past notifications, track response times, and audit your team's alert handling.
- Searchable log of all past alerts
- Filter by date range, type, severity, or asset
- Track acknowledgment and resolution status
Never miss a threat
Real-time alerts ensure your team can respond to security changes within minutes, not days. Reduce your mean time to respond across the board.
- Sub-minute delivery for critical findings
- Escalation rules for unacknowledged alerts
- Digest mode for lower-priority notifications
Frequently asked questions
Answers to the most common questions about alert channels, severity filtering, and on-call integration.
Which alert channels does FortWatch support?+
FortWatch delivers alerts through three first-class channels: email (with full finding context and remediation links), Slack (per-channel routing with severity color coding), and webhooks (JSON payloads for PagerDuty, Opsgenie, Microsoft Teams, Discord, or any custom endpoint). You can enable any combination — most teams run Slack for visibility, email for the record, and webhooks for on-call escalation.
How does FortWatch prevent alert fatigue?+
Alert fatigue is the single biggest reason monitoring tools get muted. FortWatch fights it three ways: severity filtering so you only get paged on what matters, intelligent deduplication so the same finding doesn't re-alert every scan, and a digest mode that batches medium and low severity findings into a daily or weekly summary. Critical and high findings still arrive instantly — the noise does not.
Can I filter alerts by severity?+
Yes. Every alert rule has a severity floor: Critical only, High and above, Medium and above, or All. You can set different floors per channel — for example, page the on-call via webhook only for Critical, post to #security in Slack for High and above, and email a weekly digest of everything else. Info-severity findings are never alerted by default; they require explicit opt-in.
Does FortWatch support quiet hours and on-call rotations?+
Yes. Quiet hours suppress non-critical alerts outside your team's working hours and queue them for the next business day — Critical findings still page immediately. For on-call rotation, use the webhook channel to route alerts into PagerDuty or Opsgenie, which handle the schedule, escalation policy, and acknowledgment flow. FortWatch stays the source of truth for the finding; your on-call tool handles the human side.
What's the difference between real-time alerts and digest mode?+
Real-time alerts fire within seconds of a scan detecting a new finding — use them for Critical and High severity where minutes matter. Digest mode batches lower-severity findings into a single email or Slack post delivered on your schedule (daily at 9am, end of week, etc.). Most teams run both: real-time for the urgent, digest for the ambient awareness.
Can I create custom alert rules?+
Yes. Rules can filter by severity, asset (specific domains or IPs), finding category (SSL, exposed ports, vulnerabilities, headers, etc.), and workspace. You can route different rule sets to different channels — for example, SSL expirations to the ops webhook, new CVEs to the security Slack channel, and a weekly digest of everything to the compliance mailbox.
Is there rate limiting on alerts?+
Yes. FortWatch rate-limits alerts per channel to protect against storm scenarios — if a misconfiguration suddenly exposes 200 findings, you get one summary alert instead of 200 individual pages. Deduplication also prevents the same open finding from re-alerting on every subsequent scan; you'll only hear about it again if its state changes (severity increases, asset scope changes, or it's closed and reopens).
Is every alert logged and searchable?+
Yes. Every alert that fires — plus every alert that was suppressed by a rule, quiet hours, or dedup — is logged with timestamp, channel, recipient, severity, related finding, and delivery status. The log is searchable by date, severity, channel, and asset, so you can answer 'did we alert on this before the incident?' during a post-mortem or audit review.
Secure your entire stack today
Start scanning in under 5 minutes. No credit card required. 14-day free trial included.